Example
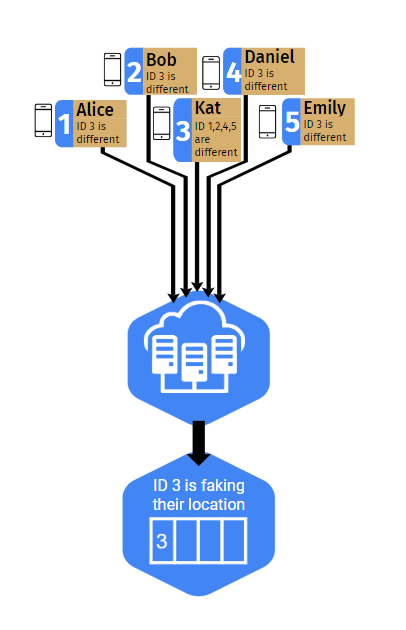
This diagram represents an example of our project in action.
It is the same example used in the video demonstration.
There are 5 users with IDs labeled 1 through 5 and a name next to them for convenience.
These users are all physically at UCSD and are physically near each other.
All of them except for Kat (ID 3) claim to be at UCSD. Kat is instead claiming to be in New York.
With our app running the users' phones are exchanging ID and location data between each other.
Each device adds an ID to a list if the other ID has a different location than the current device.
So in this case Alice and Bob have the same location so Alice does NOT add Bob's ID.
However, Kat and Alice have different locations, so Alice's phone adds Kat's ID to its list and Kat's phone adds Alice's ID to its list.
Repeating this accross all the users, everyone adds Kat (ID 3) to their list, while Kat adds every other user.
Now this data is sent to the server.
Every hour, the server will attempt to update its blacklist with new data.
At this time a majority vote is taken and determines which users are lying about their location.
In our example, Kat recieves 4 votes and every other user recieves 1.
Converting these to percentages, Kat had 80% of users claim that she was lying about her location so her ID is added to the blacklist.
The rest of the users only had 20% of users claim they were lying so they are not added to the blacklist.
Now the blacklist has been updated and the app can verify users using that information.
Project Info
Many applications make use of location data in order to provide their services, but malicious users can disrupt these by manipulating or faking their location. In an effort to combat and catch these users, our project involves a system to authenticate user location data without having one central authority in control of all the information. By leveraging the physical proximity necessary for devices to send and receive data through Bluetooth Low Energy signals, our system is able to detect users lying about their location without receiving any location information. Our portion of the project was creating the server backend that communicates with devices to store information about flagged users and process it for the purpose of adding malicious users to a blacklist. More technical details can be found in our report. You can find the link for the report on the side navigation
About us
Hello, and thanks for taking an interest in our project. This site was part of our
Data Science 180 Capstone project that we worked on for 2 quarters under a mentor.
The first quarter consisted of recreating results, exploring a domain, and proposing
a project that would then be completed in the second quarter. We were one of 66
project groups in the 2022-2023 iteration of the class. A full list of all the
teams can be found on the HDSI Showcase.
Our project is unique in that it consists of 2 teams under the same mentor:
one for the app (Group B16-2) and one for the server (Group B16-1). We are
the server-side team and consist of 4 members: Nathan Ahmann, Mason Chan,
Alex Guan, and Alan Miyazaki. Our mentor was Haojian Jin. Over the course
of this quarter, we developed a backend server (on this website) and successfully
linked it to the Android devices running the app team's code. Together these create a fully functioning system
FAQ
- What is decentralized location consensus?
- Decentralized Location Consensus means verifying users are at the location they claim to be. The decentralized part is saying that not all of the data should be stored in one place which helps protect privacy. The location consensus is that devices should reach a consensus of who is being truthful about their location.
- Why does it matter whether or not a location consensus is centralized?
- By establishing a decentralized location consensus, we are able to avoid one central entity receiving all data that is being processed. This allows for more data privacy when contacting our server, as not all information regarding the users will be in one singular location.
- Is there a real world example of how a decentralized location consensus would be beneficial?
- Location authentication is critical for several different mobile applications which rely on the position of the user for its services. Additionally, ensuring that the location consensus is decentralized will help with user privacy, as there would be no one single entity that has access to all information. For example, if the food app Grubhub were to implement a system like this, it would mean that drivers would never have to worry about customers lying about their current location. This would also mean customers would never need to worry about a data breach of Grubhub, which could compromise the location information of thousands of users.
- What were some of the greatest challenges of this project on the server side?
- Determining what kind of information clients would send to the server was an early hurdle for the team, as we were not exactly sure how the server would be able to process the data. We considered different hash functions, lists, strings, etc. before deciding that a JSON object with ID information was the best option.
- Why did your project split into 2 groups?
- In order to implement a decentralized location consensus, our project was essentially split into two main groups. The client side team would focus on the development of a mobile application, which could communicate with other users via Bluetooth Low Energy signals. The server side team (us) worked on creating a server that would look at interactions between clients and determine which users could be authenticated or blacklisted. Both sides of the project are quite involved, so having two different teams was appropriate.
- Why is this a data science project?
- The core component of our project is data privacy, which is always critical in the practice of data science. Understanding ethical practices regarding data collection is important at all times, due to safety concerns and the protection of individual privacy. While our project may not be running regression or exploring machine learning like other data science projects, it still demonstrates a main principle of the discipline which involves data collection and personal safety.